Password-stealing Linux malware served for 3 years and nobody seen

[ad_1]

Getty Photographs | posteriori
A obtain website surreptitiously served Linux customers malware that stole passwords and different delicate data for greater than three years till it lastly went quiet, researchers mentioned on Tuesday.
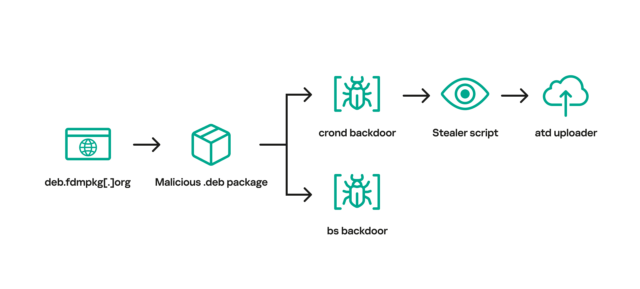
The positioning, freedownloadmanager[.]org, provided a benign model of a Linux providing referred to as the Free Obtain Supervisor. Beginning in 2020, the identical area at occasions redirected customers to the area deb.fdmpkg[.]org, which served a malicious model of the app. The model out there on the malicious area contained a script that downloaded two executable recordsdata to the /var/tmp/crond and /var/tmp/bs file paths. The script then used the cron job scheduler to trigger the file at /var/tmp/crond to launch each 10 minutes. With that, gadgets that had put in the booby-trapped model of Free Obtain Supervisor have been completely backdoored.
After accessing an IP tackle for the malicious area, the backdoor launched a reverse shell that allowed the attackers to remotely management the contaminated machine. Researchers from Kaspersky, the safety agency that found the malware, then ran the backdoor on a lab machine to look at the way it behaved.
“This stealer collects information corresponding to system data, shopping historical past, saved passwords, cryptocurrency pockets recordsdata, in addition to credentials for cloud companies (AWS, Google Cloud, Oracle Cloud Infrastructure, Azure),” the researchers wrote in a report on Tuesday. “After gathering data from the contaminated machine, the stealer downloads an uploader binary from the C2 server, saving it to /var/tmp/atd. It then makes use of this binary to add stealer execution outcomes to the attackers’ infrastructure.”
The picture beneath illustrates the an infection chain.
Kaspersky
After looking out social media posts that mentioned Free Obtain Supervisor, the researchers discovered that some individuals who visited freedownloadmanager[.]org obtained a benign model of the app, whereas others have been redirected to one of many following malicious domains that served the booby-trapped model.
- 2c9bf1811ff428ef9ec999cc7544b43950947b0f.u.fdmpkg[.]org
- c6d76b1748b67fbc21ab493281dd1c7a558e3047.u.fdmpkg[.]org
- 0727bedf5c1f85f58337798a63812aa986448473.u.fdmpkg[.]org
- c3a05f0dac05669765800471abc1fdaba15e3360.u.fdmpkg[.]org
It’s unclear why some guests obtained the non-malicious model of the software program and others have been redirected to a malicious area. The malicious redirects led to 2022 for unknown causes.
The backdoor is an up to date model of malware tracked as Bew, which was revealed in 2014. Bew was one of many elements utilized in an assault in 2017. The stealer referred to as by the backdoor was installed in a 2019 campaign after first exploiting a vulnerability within the Exim Mail Server.
“Whereas the marketing campaign is at the moment inactive,” the researchers wrote, referring to the latest incident, “this case of Free Obtain Supervisor demonstrates that it may be fairly tough to detect ongoing cyber assaults on Linux machines to the bare eye.” They added:
The malware noticed on this marketing campaign has been recognized since 2013. As well as, the implants turned out to be fairly noisy, as demonstrated by a number of posts on social networks. In line with our telemetry, victims of this marketing campaign are positioned everywhere in the world, together with Brazil, China, Saudi Arabia and Russia. Given these information, it could appear paradoxical that the malicious Free Obtain Supervisor package deal remained undetected for greater than three years.
- Versus Home windows, Linux malware is way more not often noticed;
- Infections with the malicious Debian package deal occurred with a level of chance: some customers obtained the contaminated package deal, whereas others ended up downloading the benign one;
- Social community customers discussing Free Obtain Supervisor points didn’t suspect that they have been brought on by malware.
The submit presents quite a lot of file hashes and area and IP addresses that folks can use to point in the event that they’ve been focused or contaminated within the marketing campaign, which the researchers suspect was a provide chain assault involving the benign model of Free Obtain Supervisor. The researchers mentioned individuals working the freedownloadmanager[.]org website didn’t reply to messages notifying them of the marketing campaign. In addition they didn’t reply to an inquiry for this submit.
[ad_2]
Source



