Microsoft profiles new menace group with uncommon however efficient practices

[ad_1]

Microsoft has been monitoring a menace group that stands out for its potential to money in from knowledge theft hacks that use broad social engineering assaults, painstaking analysis, and occasional bodily threats.
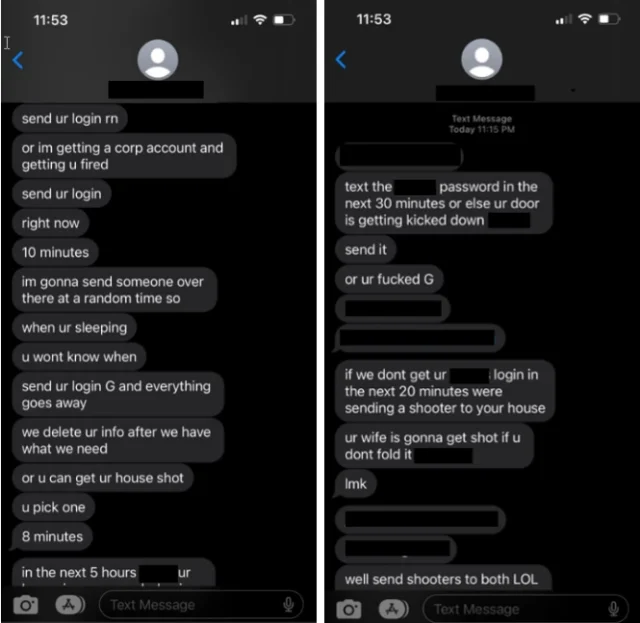
In contrast to many ransomware assault teams, Octo Tempest, as Microsoft has named the group, doesn’t encrypt knowledge after gaining unlawful entry to it. As an alternative, the menace actor threatens to share the info publicly until the sufferer pays a hefty ransom. To defeat targets’ defenses, the group resorts to a number of methods, which, in addition to social engineering, consists of SIM swaps, SMS phishing, and dwell voice calls. Over time, the group has grown more and more aggressive, at occasions resorting to threats of bodily violence if a goal doesn’t adjust to directions to show over credentials.
“In uncommon situations, Octo Tempest resorts to fear-mongering techniques, focusing on particular people by means of cellphone calls and texts,” Microsoft researchers wrote in a post on Wednesday. “These actors use private data, comparable to residence addresses and household names, together with bodily threats to coerce victims into sharing credentials for company entry.”
Microsoft
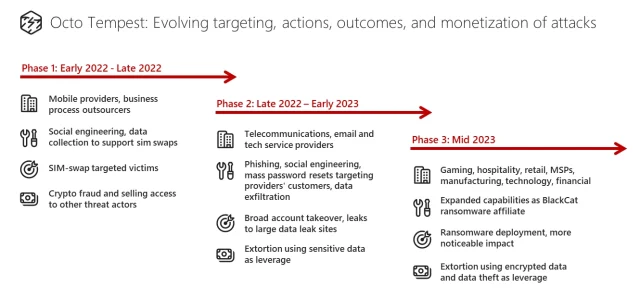
Octo Tempest first got here to note early final yr because it used SIM swaps to ensnare corporations that present cellular telecommunications processing companies to different corporations. The group would then promote the unauthorized entry it gained by means of these swaps to different crime teams or use them to carry out account takeovers of high-net-worth people to steal their cryptocurrency. By the tip of the yr, the group had broadened its methods and expanded its targets to incorporate cable telecommunications, e-mail, and know-how organizations. Round this time, it started extorting victims whose knowledge it had stolen, typically resorting to bodily threats.
Earlier this yr, the native-English-speaking group turned an affiliate of the ALPHV/BlackCat ransom-as-a-service operation. That made the group stand out since Jap European ransomware crime syndicates hardly ever settle for English-speaking members. Octo Tempest’s ALPHV/BlackCat ransomware assaults goal each Home windows and Linux variations programs, usually once they run on VMWare ESXi servers. Targets usually are in industries together with pure sources, gaming, hospitality, shopper merchandise, retail, managed service suppliers, manufacturing, legislation, know-how, and monetary companies.
Microsoft
“In current campaigns, we noticed Octo Tempest leverage a various array of TTPs to navigate advanced hybrid environments, exfiltrate delicate knowledge, and encrypt knowledge,” Microsoft wrote. “Octo Tempest leverages tradecraft that many organizations don’t have of their typical menace fashions, comparable to SMS phishing, SIM swapping, and superior social engineering methods.”
The researchers continued:
Octo Tempest generally launches social engineering assaults focusing on technical directors, comparable to help and assist desk personnel, who’ve permissions that would allow the menace actor to realize preliminary entry to accounts. The menace actor performs analysis on the group and identifies targets to successfully impersonate victims, mimicking idiolect on cellphone calls and understanding private identifiable data to trick technical directors into performing password resets and resetting multifactor authentication (MFA) strategies. Octo Tempest has additionally been noticed impersonating newly employed workers in these makes an attempt to mix into regular on-hire processes.
Octo Tempest primarily beneficial properties preliminary entry to a corporation utilizing certainly one of a number of strategies:
- Social engineering
- Calling an worker and socially engineering the person to both:
- Set up a Distant Monitoring and Administration (RMM) utility
- Navigate to a web site configured with a faux login portal utilizing an adversary-in-the-middle toolkit
- Take away their FIDO2 token
- Calling a corporation’s assist desk and socially engineering the assistance desk to reset the person’s password and/or change/add a multi-factor authentication token/issue
- Buying an worker’s credentials and/or session token(s) on a legal underground market
- SMS phishing worker cellphone numbers with a hyperlink to a web site configured with a faux login portal utilizing an adversary-in-the-middle toolkit
- Utilizing the worker’s pre-existing entry to cellular telecommunications and enterprise course of outsourcing organizations to initiate a SIM swap or to arrange name quantity forwarding on an worker’s cellphone quantity. Octo Tempest will provoke a self-service password reset of the person’s account as soon as they’ve gained management of the worker’s cellphone quantity.
Extra tradecraft consists of:
- PingCastle and ADRecon to carry out reconnaissance of Lively Listing
- Superior IP Scanner to probe sufferer networks
- Govmomi Go library to enumerate vCenter APIs
- PureStorage FlashArray PowerShell module to enumerate storage arrays
- AAD bulk downloads of customers, teams, and gadgets.
Microsoft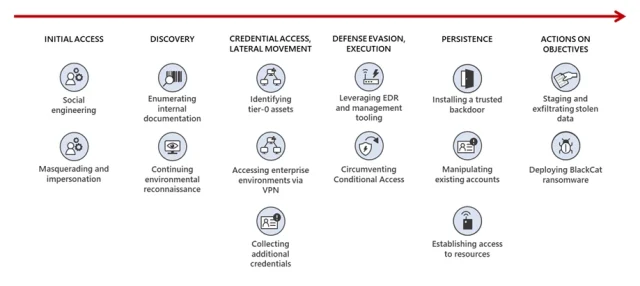
Microsoft’s submit accommodates numerous different particulars, together with defenses organizations can undertake to repel the assaults. Defenses embrace utilizing out-of-band communications when interacting with co-workers, educating workers, and implementing FIDO-compliant multifactor authentication.



